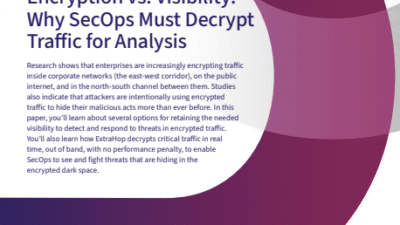
How to Embrace Advanced Encryption Without Introducing Risk
How to Embrace Advanced Encryption Without Introducing Risk How to Embrace Advanced Encryption Without Introducing Risk Encryption is…
How to be a Better Threat Hunter
How to be a Better Threat Hunter How to be a Better Threat Hunter Stop Guessing—Start Hunting Smarter Learn how to leverage network data to…
From the C-Suite to the SOC: Consolidating the Network Security Solutions
From the C-Suite to the SOC: Consolidating the Network Security Solutions From the C-Suite to the SOC: Consolidating the Network Security…
The Rise of Platform Engineering
The Rise of Platform Engineering The Rise of Platform Engineering Just like a well-managed launch site for a space-bound rocket, platform…
Complexity vs. Capability: Navigating The Kubernetes Conundrum
Complexity vs. Capability: Navigating The Kubernetes Conundrum Complexity vs. Capability: Navigating The Kubernetes Conundrum Wondering if…
Balancing Kubernetes Costs and Performance with Observability
Balancing Kubernetes Costs and Performance with Observability Balancing Kubernetes Costs and Performance with Observability A global Morning…
Quick Guide: 6 Key Steps for Kubernetes Troubleshooting
Quick Guide: 6 Key Steps for Kubernetes Troubleshooting Quick Guide: 6 Key Steps for Kubernetes Troubleshooting Kubernetes environments are…
Troubleshooting Kubernetes Environments with Observability
Troubleshooting Kubernetes Environments with Observability Troubleshooting Kubernetes Environments with Observability Kubernetes complexity is…
The Economics of Observability Data: How to Correct 3 Common Log Management Mistakes
The Economics of Observability Data: How to Correct 3 Common Log Management Mistakes The Economics of Observability Data: How to Correct 3…
Rising to the challenge: 8 real-life customer solutions
Rising to the challenge: 8 real-life customer solutions Rising to the challenge: 8 real-life customer solutions The most impactful IT teams…